Third-Party Cybersecurity, Shaped for Your Risk DNA
Trusted by the Most Complex Supply Chains in the World
Unlock the Cyber Fingerprint of Every Third-Party
For every third-party connection, Panorays assigns a real-time rating – a unique Risk DNA. This dynamic rating allows you to continuously adapt your security measures, guiding each relationship towards its optimal security posture.
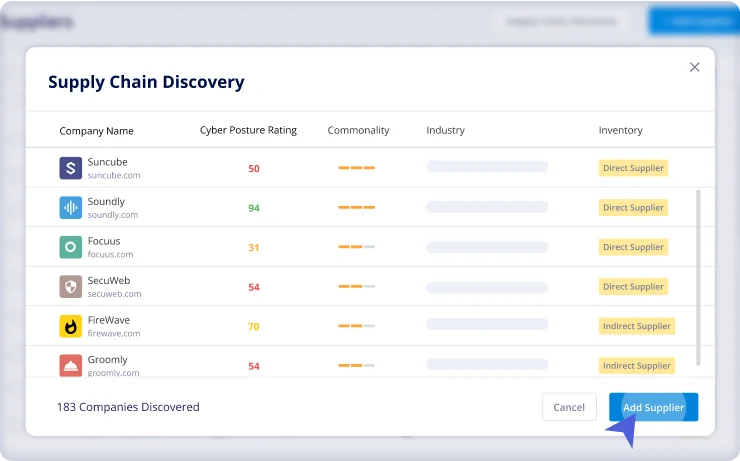
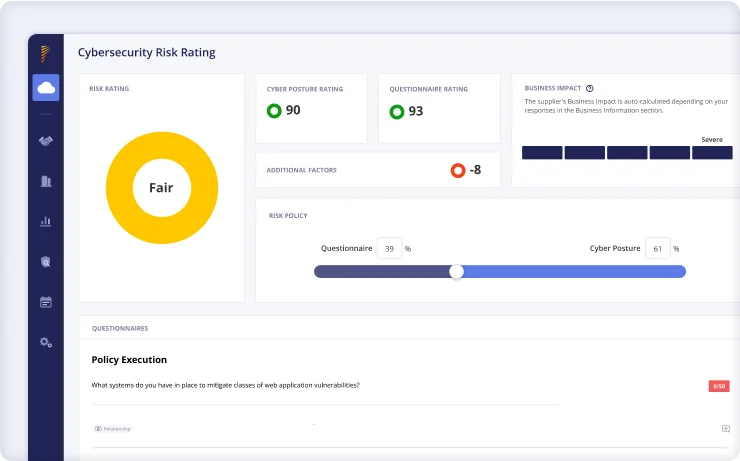
Create Cyber Risk Assessments Based on Real Business Risk
Find the security sweet spot for each business connection. Panorays tailors external attack surface assessments and internal risk assessments to each unique relationship, pinpointing risks that can impact your business. Focus your security efforts where they matter most, and gain boardroom approval with clear, actionable insights.
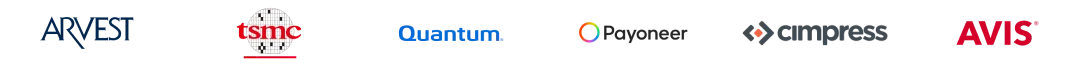
Gain Control With Continuous Supply Chain Detection and Monitoring
Uncover hidden risks across your network. Panorays AI maps and ranks all 3rd to Nth-party connections, based on your evolving Risk DNA. Real-time alerts instantly notify you of any changes to your or your third parties’ cyber posture, enabling immediate action to neutralize emerging threats.
Act on What Matters With Actionable Threat Alerts
Filter evolving third-party threats through your company’s risk lens. Panorays prioritizes vulnerabilities based on your KPIs and KRIs, delivering actionable alerts with clear context and next steps. Go from alert to action in seconds, assign tasks, and track progress from one dedicated Incident Response Portal.
Fast-Track Remediation With Vendor Self-Guiding Plans
Close critical security gaps from day one. Panorays tailors prioritized action plans for each vendor, focusing on the risks that could impact you the most. Easily track and monitor progress as Panorays automatically updates and reflects changes to your third-party security measures.
Reduce the Likelihood of a Third-Party Breach
Supply Chain Visibility
Panorays detects your entire threat landscape and immediately alerts you of vulnerabilities and breaches. You can easily respond to threats in collaboration with your third parties, keep an audit of all communication, and close security gaps with suggested remediation steps.
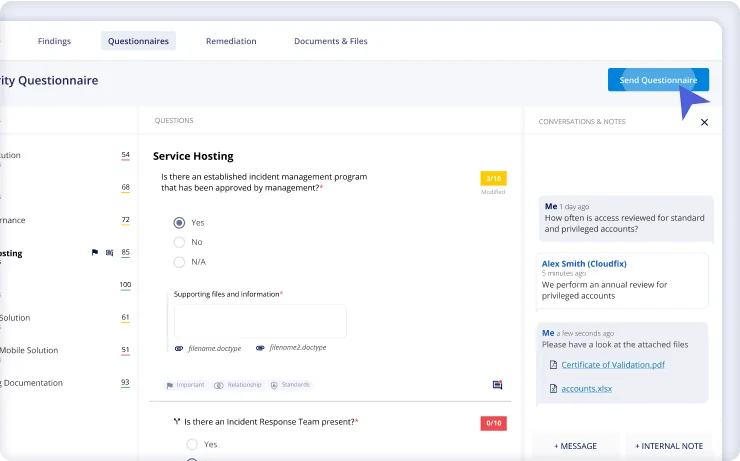
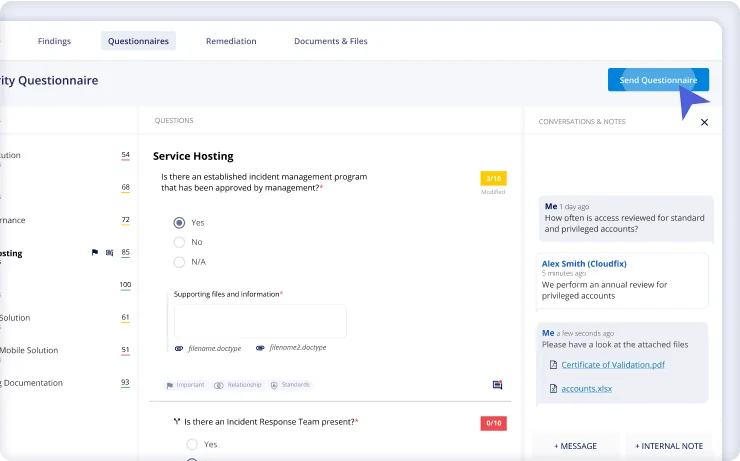
Automated Third-Party Cyber Risk Management
Streamline third-party questionnaires with compliance templates, autocomplete responses, and AI-powered questionnaire validations. Speed up vendor assessments by auto-assigning team members for their review, and setting rules to approve or reject vendors automatically.
Comprehensive Risk Assessments
Go deeper with contextual, AI-powered risk assessments, reflecting questionnaire accuracy, cyber posture, and business impact. Our dynamic rating adapts to your changing Risk DNA, letting you mitigate threats before they escalate into breaches.
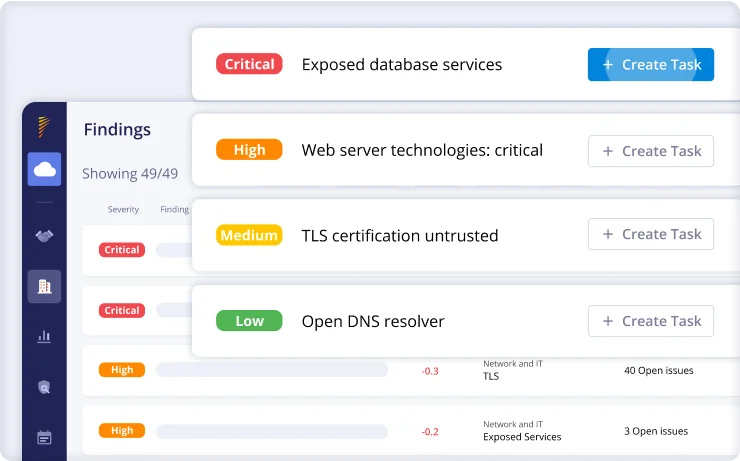
External Attack Surface Management
Protect your organization from cyber threats with external attack surface monitoring. Get immediate alerts on security gaps found in your digital assets and respond to any third-party vulnerabilities.
-
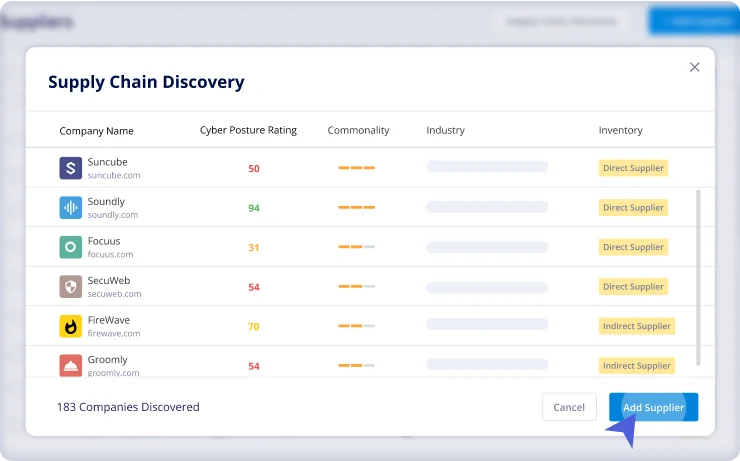
Supply Chain Visibility
Panorays detects your entire threat landscape and immediately alerts you of vulnerabilities and breaches. You can easily respond to threats in collaboration with your third parties, keep an audit of all communication, and close security gaps with suggested remediation steps.
-
Automated Third-Party Cyber Risk Management
Streamline third-party questionnaires with compliance templates, autocomplete responses, and AI-powered questionnaire validations. Speed up vendor assessments by auto-assigning team members for their review, and setting rules to approve or reject vendors automatically.
-
Comprehensive Risk Assessments
Go deeper with contextual, AI-powered risk assessments, reflecting questionnaire accuracy, cyber posture, and business impact. Our dynamic rating adapts to your changing Risk DNA, letting you mitigate threats before they escalate into breaches.
-
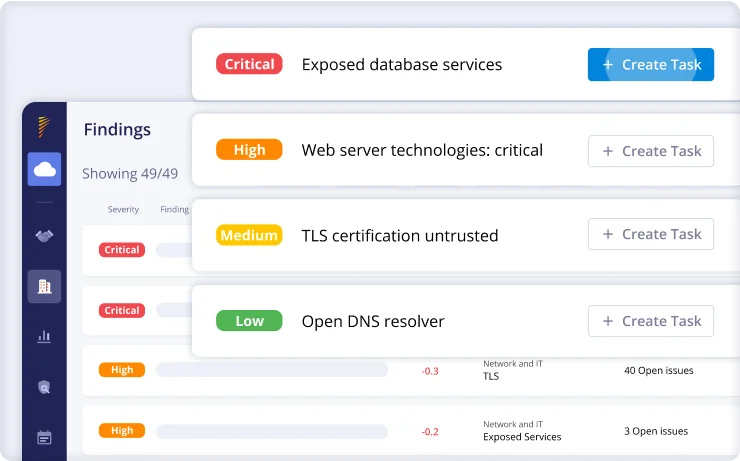
External Attack Surface Management
Protect your organization from cyber threats with external attack surface monitoring. Get immediate alerts on security gaps found in your digital assets and respond to any third-party vulnerabilities.


