If your organization is like most, it depends on vendors, suppliers and business partners to help get work done. But when these often-less-secure third parties connect to your systems, you effectively increase your organization’s attack surface, thereby making yourself more vulnerable to cyberattacks. This problem is exacerbated when considering cloud assets: Your third parties may be storing your data on the cloud without proper configuration, but how would you ever know?
To address this problem, Panorays recently introduced a new cloud category to our cyber assessments of third parties, which evaluates how third parties manage their data with cloud services. In particular, it checks whether:
- Specific cloud services are exposed to the public
- Cloud services reside in a single geographic region
- Cloud services host a website within a cloud storage bucket, such as AWS S3
- Cloud services have a public listing enabled for a cloud storage bucket
All of the above are red flags of possible cloud issues and misconfigurations. They could result in data leaks or breaches that expose private data, leaving your organization open to regulatory penalties and loss of customer trust.
Panorays researchers tested thousands of its suppliers to gather data about the findings from this new cloud assessment. Here is what we discovered:
1. The Vast Majority of Suppliers Use the Cloud
We intuitively know that cloud providers such as Amazon AWS, Microsoft Azure and Google GCP have become an integral part of the computing backbone of most organizations. Even traditional industries that may hesitate to make the transition rely heavily on cloud providers for services such as marketing, support and operations.
This was confirmed by the data that we uncovered. Panorays tested thousands of suppliers; of which 84% were found to use cloud services.
2. A Variety of Industries Use the Cloud
The primary suppliers using the cloud are in industries that you might expect: computer software, information technology, internet software and financial services. Yet there are some surprises: Here are 20 industries and their cloud adoption percentage.
3. Cloud Use Varies by Location
We found that suppliers in countries across the world have varying usage of the cloud. Here are the locations with the highest cloud usage.
4. Cloud Single Region Is the Most Prevalent Issue
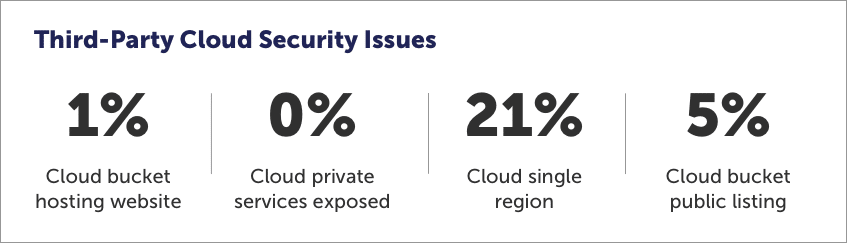
While the majority of companies appear to have secure cloud security, we found 27% with issues, including 21% that have cloud storage in a single region. This is not surprising, since it’s cheaper and easier for companies to deploy single-region architecture. However, this practice can be problematic when faced with disaster recovery, which is why it’s not recommended.
5. Cloud Bucket Public Listings Are the Most Surprising Issue
We discovered 5% of suppliers with a public listing for a cloud storage bucket.
The public listing for cloud storage buckets was unexpected, considering that open buckets remain a pressing problem that has gained a great deal of publicity lately. In a recent case, for example, a business-to-business platform for supply chain automation reportedly exposed 2.5 million files carrying customer data because of a misconfigured AWS S3 bucket. These types of incidents occur frequently, so it’s interesting to note that many companies have still not taken the necessary steps for prevention.
Want to learn more about Panorays’ new cloud category and how it can help you manage third-party security risk? Schedule a demo today.





